- Access Privileges For Macnextlasopa Parents
- Access Privileges For Macnextlasopa Visa
- Access Privileges For Macnextlasopa Disabled
- Access Privileges For Macnextlasopa Travel
- Access Privileges For Macnextlasopa Students
- Access Privileges For Macnextlasopa Patients
- Access Privileges For Macnextlasopa Credit Card
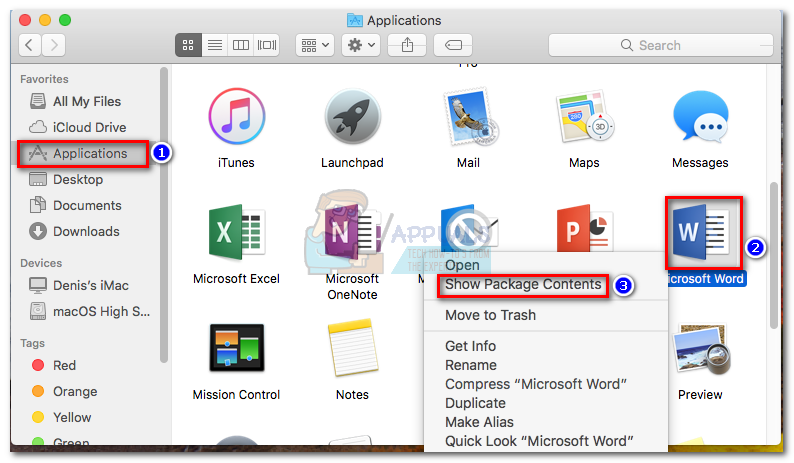
Subscribe Now:More:access privileges on a Mac will r.

MAC-Based Access Control is one method for preventing unauthorized access to the Wireless LAN. This article discusses how MAC-Based Access Control works and provides step-by-step configuration instructions for Microsoft NPS and Dashboard.
Access Privileges For Macnextlasopa Parents
MAC-Based Access Control
It is critical to control which devices can access the wireless LAN. MAC-Based Access Control can be used to provide port based network access control on MR series access points. With MAC-Based Access Control, devices must be authenticated by a RADIUS server before network access is granted on an SSID. The AP (RADIUS client) sends a RADIUS Access-Request to the RADIUS server containing the username and password of the connecting wireless device. The username and password combination is always the MAC address of the connecting device, lower case without delimiting characters. If a RADIUS policy exists on the server that specifies the device should be granted access and the credentials are correct, the RADIUS server will respond with an Access-Accept message. Upon receiving this message, the AP will grant network access to the device on the SSID. If the RADIUS server replies with an Access-Reject because the device does not match a policy, the AP will not grant network access. Below is a diagram showing a successful authentication.
- Select Full Disk Access on the left side. Leave this window open. In the pop-up, drag the icon to the Full Disk Access area you have open. This will add all the entries needed. Manually adding permissions The following can be performed on macOS 10.14+.
- Tech support scams are an industry-wide issue where scammers trick you into paying for unnecessary technical support services. You can help protect yourself from scammers by verifying that the contact is a Microsoft Agent or Microsoft Employee and that the phone number is an official Microsoft global customer service number.
- Subscribe Now:More:access privileges on a Mac will r.
- Elevating Privileges Safely. By default, applications run as the currently logged in user. Different users have different rights when it comes to accessing files, changing systemwide settings, and so on, depending on whether they are admin users or ordinary users.
MAC-Based Access Control has some security implications which must be considered. One is that it is not an association method that supports wireless encryption. Therefore clients will need to rely on upper layer protocols for encrypting traffic such as SSL or IPsec once a device has gained network access. The second being the credentials used. Because the MAC address of the device is used as the credentials, an attacker can easily gain network access by spoofing the MAC address of previously authenticated clients. Below are the steps necessary in order, to deploy MAC-Based Access Control using Microsoft NPS.
The world faces more and more data breaches caused by lost or stolen credentials. How to manage network user accounts in order to protect corporate data?
Many companies do not track how their employees use shared privileged credentials and do not engage in privileged user monitoring. Instead, these organizations set tough frames for personal accountability within their facilities. According to a study by Gartner, improper privileged access management will be the major cause of about 60% of data breach incidents by 2018 compared to 40% in 2015.
To access a user directory service account with administrator privileges, hackers may apply spear phishing, the Pass the hash method, or other methods.
In an organization, there are different types of privileged accounts, categorized by the task they perform:
- administrative accounts (have access to all standard privileged processes);
- system accounts (are integrated into applications or systems, e.g. Windows or Linux);
- operational accounts (include shared accounts for software administration or installation and service accounts for remote access to systems).
Companies should be aware of possible outsider and insider attacks on these accounts and strive to improve control measures for users with privileged access permissions. In this article, we will cover the best practices of the privileged access management(PAM).
Tip #1: Make a List of All Privileged Access Accounts
To ensure accountability for all privileged accounts in your organization, you should inventory them, especially if you used dynamic environments. To accurately list such accounts, you may use the autodiscovery feature provided by various PAM solutions. Furthermore, your list should contain detailed information about owners of privileged accounts and their roles. This technique will allow you to monitor who is responsible for a particular account and prevent an unauthorized access for employees that no longer work in your company.
Tip #2: Don’t Share Passwords for Shared Accounts
Access Privileges For Macnextlasopa Visa
While this practice seems to be quite obvious, some administrators insist that sharing shared-account passwords among approved users can’t lead to negative consequences. However, this approach makes proper personal accountability impossible and violates regulatory compliance requirements. Furthermore, it increases a probability of revealing these passwords to others. Therefore, you should ensure that shared-account passwords are accessible only to account owners. To avoid revealing shared-account passwords, you should consider implementing the single sign-on (SSO) authentication. In case you need to reveal a password, you have to change it after use.
Tip #3: Use as Few Privileged Accounts as Possible
To reduce risks of data thefts, you should minimize the number of account with a privileged access or even eliminate all accounts with permanent and full privileges if possible. The same practice is applicable when it comes to shared privileged accounts that are hard to account for. It is impossible to define a concise appropriate number of accounts with privileged access, but they should be as few as possible in case you want to get a better control them.
Tip #4: Minimize the Number of Rights for Each Privileged Account
To better protect your data from disclosure and ensure the proper superuser privilege management, you should set minimum rights needed for specific users so as they could perform their obligations. Establish a well-controlled use of privileged accounts. Every such account should have minimum privileges that are necessary to accomplish specific tasks. It means that if a specific account is assigned for application administration, then it shouldn’t have system permissions beyond the scope of configuring or restarting said app. Therefore, you shouldn’t enable this account on those systems that have doesn’t have the app in question running.
Access Privileges For Macnextlasopa Disabled
Tip #5: Manage Passwords Properly
To reduce risks of compromising privileged accounts, you should manage passwords wisely. They should be complex, unique, regularly changed, and never shared. It will ensure a better protection for sensitive data and keep out ordinary user accounts from the ones with privileged access. Make sure these passwords are individual to all privileged users and unique for each account or app. Furthermore, never store passwords unencrypted so that no one can compromise them.
Tip #6: Separate Privileges for Specific Tasks
You should split up privileges necessary to accomplish specific tasks among various administrators. It will allow you to ensure that those admins won’t have conflicting privileges. Since superuser administrative privileges provide users with full access to data and operations, divided privileges will reduce a risk if users with privileged access ever to perform malicious actions.
Tip #7: Practice Privilege Elevation Instead of Assigning Superuser Privileges
Administrators usually utilize personal accounts without privileged permissions to accomplish their ordinary tasks, such as surfing the Internet, working with their emails, using corporate applications, etc. Instead of granting administrators with a full access, use privileged elevation to allow them to perform corresponding actions when needed. Such temporary privileged access will significantly reduce data theft threats.
Tip #8: Use One-Time Passwords
The advantage of a one-time password (OTP) over a static one is that the password can not be reused. Thus, an attacker who intercepts data from a successful authentication session can’t use the copied password to get access to the protected information system. However, using OTPs, you can’t protect your system from attacks based on an active interference in the communication channel used for authentication, e.g. “man in the middle” attacks. Although, it will increase security within user authentication.
Access Privileges For Macnextlasopa Travel
Tip #9: Use Two-Factor Authentication
The double-layered protection will ensure secure authentication and make it more difficult for third parties to intercept your data. Unlike a traditional logging process only with a username or password (knowledge factors), two-factor authentication also includes possession factors (physical tokens, SMS, biometrics, etc.) to let users access to an account. Two-factor authentication forms an additional barrier for hackers striving to get administrative privileges in order to access corporate applications and data. Without physical access to person’s phone or security token, hackers will be unable to authenticate.
Tip #10: Record Privileged User Sessions
In fact, proper privileged access management is not enough for ensuring a high security level for your corporate systems. To timely detect suspicious activities and efficiently investigate malicious operations, you should record privileged user sessions. By reviewing these sessions, you will be able to see all performed actions within their proper context, allowing you to determine whether malicious activity have taken place. User activity monitoring solutions also usually contain robust alerting functionality, allowing you to not only investigate issues after the fact, but also detect incidents as they happen and often even block ongoing sessions, preventing further damage.
How Ekran System Can Help You with Privileged Access Management
Access Privileges For Macnextlasopa Students
Ekran System is a universal insider threat detection tool that enables companies to audit activities of both regular and privileged users and protect corporate systems from data breaches. The solution can record, monitor, and audit privileged sessions as well as provides an intuitive user interface with effective search tools.
Real-time alerts will allow you to timely detect suspicious activity and block it if the session is still ongoing. Using Ekran System, you will be able to control access to monitored endpoints due to the built-in two-factor authentication feature and one-time password functionality. Furthermore, with this solution, you can depersonalize corporate shared accounts by enabling a requirement to provide personal account credentials while using shared access. Thus, you will always know who stands behind a specific shared account session.
Access Privileges For Macnextlasopa Patients

Access Privileges For Macnextlasopa Credit Card
Ekran System allows monitoring privileged user sessions while enabling you to focus on your priority security tasks and implementing other best practices for privileged access management.
